With mainstream companies such as Colonial Pipeline and JBS Foods increasingly becoming the victims of ransomware attacks, it’s only a matter of time before cyber criminals turn their attention to the cannabis industry.
Ransomware is a nefarious hack that takes control of a company’s files and data and locks out the rightful owners. The attackers gain access through phishing emails that deploy malware when unsuspecting employees click on a link. Once a ransomware attacker has taken over a company’s computer system, they typically demand cryptocurrency to return control to the owner.
While most high-profile mainstream companies have strong IT departments working to prevent ransomware attacks, many cannabis business haven’t taken the necessary steps to defend themselves, experts say.
“The majority of cannabis companies have one or two IT folks, if that – not someone with security certification,” said Ryan Ninness, vice president of technology at Lafayette, Colorado-based Urban-Gro, an integrated architecture, engineering and cultivation systems company. “They’re not monitoring or looking at the network on a daily basis.”
Cannabis companies at risk
A recent survey of MJBizDaily readers found that 59% of respondents had not taken steps to prevent ransomware attacks.
Cannabis companies are vulnerable to the attacks for several reasons, Ninness said. First, there’s the perception that marijuana businesses are flush with money. Additionally, some people find the industry distasteful and will do what they can to harm it. Finally, many hackers are seeking fame and fortune that would accompany a successful attack.
“They know it will make big news,” Ninness said.
What’s at stake
Ransomware attacks in 2020 were up 150% over the previous year, and the amounts victims paid attackers rose more than 300% during the same period, according to the Harvard Business Review.
Efforts to detect and report ransomware payments are critical to preventing and deterring future attacks as well as holding the attackers accountable for their crimes, according to the Financial Crimes Enforcement Network (FinCEN), a government agency.
“As the past few months have demonstrated, the surge in ransomware attacks threatens our critical infrastructure, municipalities and the most vulnerable among us. (It) is increasingly impacting the lives of the American people,” said Michael Mosier, FinCEN’s acting director.
Train against attacks
Each month, Urban-Gro requires employees to watch a four-minute video produced by Westlake Village, California-based security awareness and training company Ninjio. The cartoon videos about real-world security provide information about common mistakes with catastrophic impacts.
“It’s easily saved us $100,000 to $200,000 a year since we’ve launched it,” Ninness said. “Since we’ve launched (the training), we have not had a single penetration of a user.”
Ninness said he’s against paying ransom to retrieve company information but admits companies that are under siege and don’t have backups are likely to feel differently.
“Hospital systems pay because they have these big, huge systems and backups, but they never test anything,” he said. “Can a hospital be down for a week because it’s trying to store the data? That’s where it gets tempting to pay the ransom.”
Ninness said he’s not aware of any cannabis companies that have been hacked, and that troubles him.
“I’m worried that the industry looks at the fact that they haven’t been hit yet and take that as a token that they have time to wait,” he said. “They really don’t. As soon they detect that you’re a vulnerable target, you’ll get hit. It’s only going to take one (ransomware attack) to make the industry a target and vulnerable.”
Worker training
Educating employees is the No. 1 measure cannabis businesses can take to ensure their systems are secure, said a representative of a Colorado-based edibles manufacturer who asked not to be identified for fear of the company becoming a target.
“The most common way to gain access is through employees,” he said.
The edibles manufacturer has engaged KnowBe4, a Clearwater, Florida-based security training platform, to train and test its employees by sending out fake emails that should be construed as malicious to monitor how they respond.
“Everyone gets a lot of phishing emails,” he said. “But because of our training, I get people asking whether (they are) legit. The marijuana industry is heavily targeted by phishing emails. These malicious actors know that these are new companies and might not have the robust software to protect them.”
As many employees worked remotely during the coronavirus pandemic, the edibles manufacturer feared its networks were open to more ransomware threats because of its inability to properly secure every network.
“It was such a quick change with little time to prepare and not enough time to secure employees’ networks,” he said.
Stopping theft
It’s also important to educate employees about how to spot emails that might appear legitimate but actually are a scam, said Ajay Chawla, co-founder and partner in Troy, Michigan-based IT consulting firm Backcross Solutions.
Chawla shared one situation a Backcross client experienced: An employee received an email that appeared to be from the company’s CEO saying the business had just won another license. The email instructed the employee to cut a check for $15,000 and drop it off at a certain address by the end of the day.
The employee cut the check, but when he got in his car, the CEO happened to call, ultimately stopping the fraudulent activity.
“You see the email, and it almost looks exactly like your CEO’s, but (the address may be one) letter different, and you don’t recognize it,” Chawla said. “It’s things like that that happen all the time. Those kinds of email hacks are easy to do, and people often mistake them.”
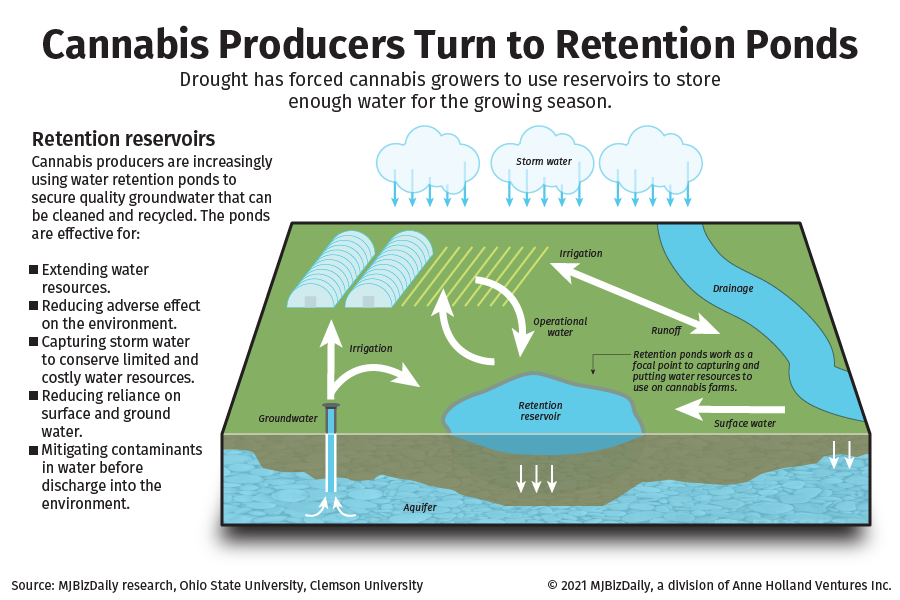
Grow operations are particularly vulnerable to cyberattacks because their irrigation, feeding and lighting systems all are connected through internet systems that aren’t difficult to breach, Chawla said.
“They have tracking systems, they have seed-to-sale (programs) in their dispensary or grow, they have a ton of physical security. So, when we ask them about security, they want to show us their camera room and their big armed guard,” Chawla said. “We try to explain that the person who’s going to come in and steal from you is not across the street or in this town, they’re in Ukraine or Russia or somewhere else.”
Backcross partner John Lamarche said that many cannabis companies are so focused on opening their retail locations and adhering to other compliance matters that IT and cybersecurity fall into the “nice to have” category.
“They’re not focusing on cyber security, and they are absolutely vulnerable,” Lamarche said. “As we get more professional money from people who see cannabis as a business opportunity and people who have a strong business background outside of cannabis, they’re reaching out to companies like ours. As the industry matures, you’ll see more people gravitate to the more sophisticated solutions.”